Recent posts
View allBest Free Website Create | Free Domain and Hosting
Website Create Various web hosting agencies provide an interface to build websites fro…
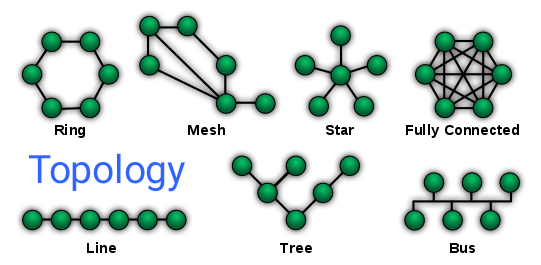
What is Mesh Topology
Mesh topology In this topology, computers are interconnected and can be connected in…
What is Ring Topology
Ring Topology As the name suggests, the ring topology will be like a spherical circl…
What is web hosting? How does it work
web hosting In addition to the name, a website contains various documents, such as ima…
Career Concept
Career Generally speaking, the specific functional part of life is a career. The acti…
Build your dream career
dream career Only people dream. Dreaming - in different colors, in different dimens…
Ways to get rid of malware
Malware Viruses, worms trojan horses, etc. can be removed by using special computer …
Types of Viruses
virus Any program must be able to execute its code and write to memory in order to r…
History of Viruses
History of viruses Computer scientist John von Neumann shed light on this in 1949, l…
What is Computer Virus
Computer virus A computer virus is a type of malicious software or malware that is cap…
Types of Malware
Malware Among the common and detected malware, the following three types of malware …
What is Star Topology
Star Topology Star Topology: If all the computers in a network are connected to a cent…
Internet use in everyday life
Internet use in everyday life There was a time when we used to ask someone if we can …
Spreadsheet
spreadsheet Since the early days of mankind, people had to keep track of various thing…
Computer Hacking
Computer hacking Hacking is defined as entering into a computer system or network wi…
Optical Fiber
Optical fiber Optical fiber is a very thin type of plastic Glass system. Light sign…
How does malware work?
malware Computer systems that have software security flaws create an opportunity for m…
Malicious software
Malicious software If you want to do any work on the computer, it has to be done throu…
How satellites Working
A communication satellite floating in space Satellite: Satellites orbit the Earth from…
What is Lan Card
A lan card Lan Card: The device that is required to connect two or more computers toge…
Introduction to the world
World 1. The estimated age of the earth is 4500 million years. 2. The area of t…
Bus Topology
Bus Topology Bus Topology: In this topology all the computers are connected along a…
What is Topology
In a computer network, many computers are connected together, the phone allows one com…
What is Hub
A Hub A hub is usually used to connect many ICT devices such as computers, printers,…
Newton's Second Law
Newton's Second Law Newton's second law is one of the most important laws in …
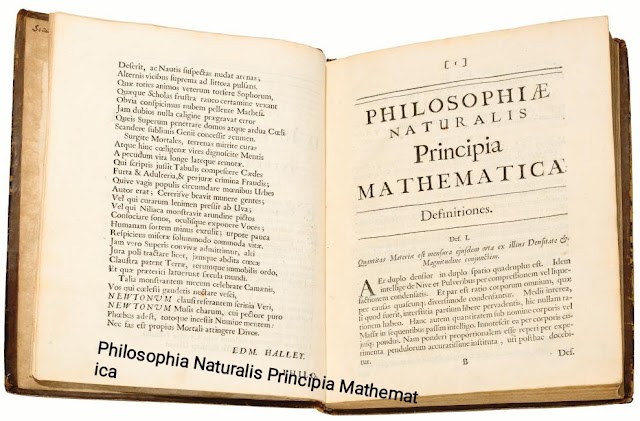
Philosophia Naturalis Principia Mathematica
Philosophia Naturalis Principia Mathematica Isaac Newton was a British physicist. Ab…
Newton's First Law
Newton Newton's First Law: Unless an external force is applied, an object at rest…
Concept of Network
If two or more computers are connected together through a means of communication, if …
Changes in Earth's Atmosphere
Changes in Earth's atmosphere Changes in Earth's atmosphere over geological …
Change of World
change of world Earth changes with the flow of time Radioisotope dating of rocks and…
Age of The Earth
age of the earth The age of the Earth compared to the universe The universe is still …
What is Cyber Crime
Cyber Crimes Cyber Crime: Any act against society and law is a crime. And the crimes…
DDos Attack
DDos Attack When a person is interviewed on TV, if many people ask the person many q…
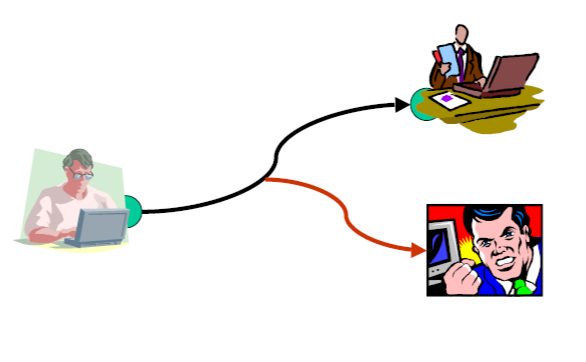
Data interception
Data Interception Almost all of us have seen the irrigation of land from water pumps…
Popular Posts

DDos Attack

Today Live Match Cricket

What is Mesh Topology































Social Media